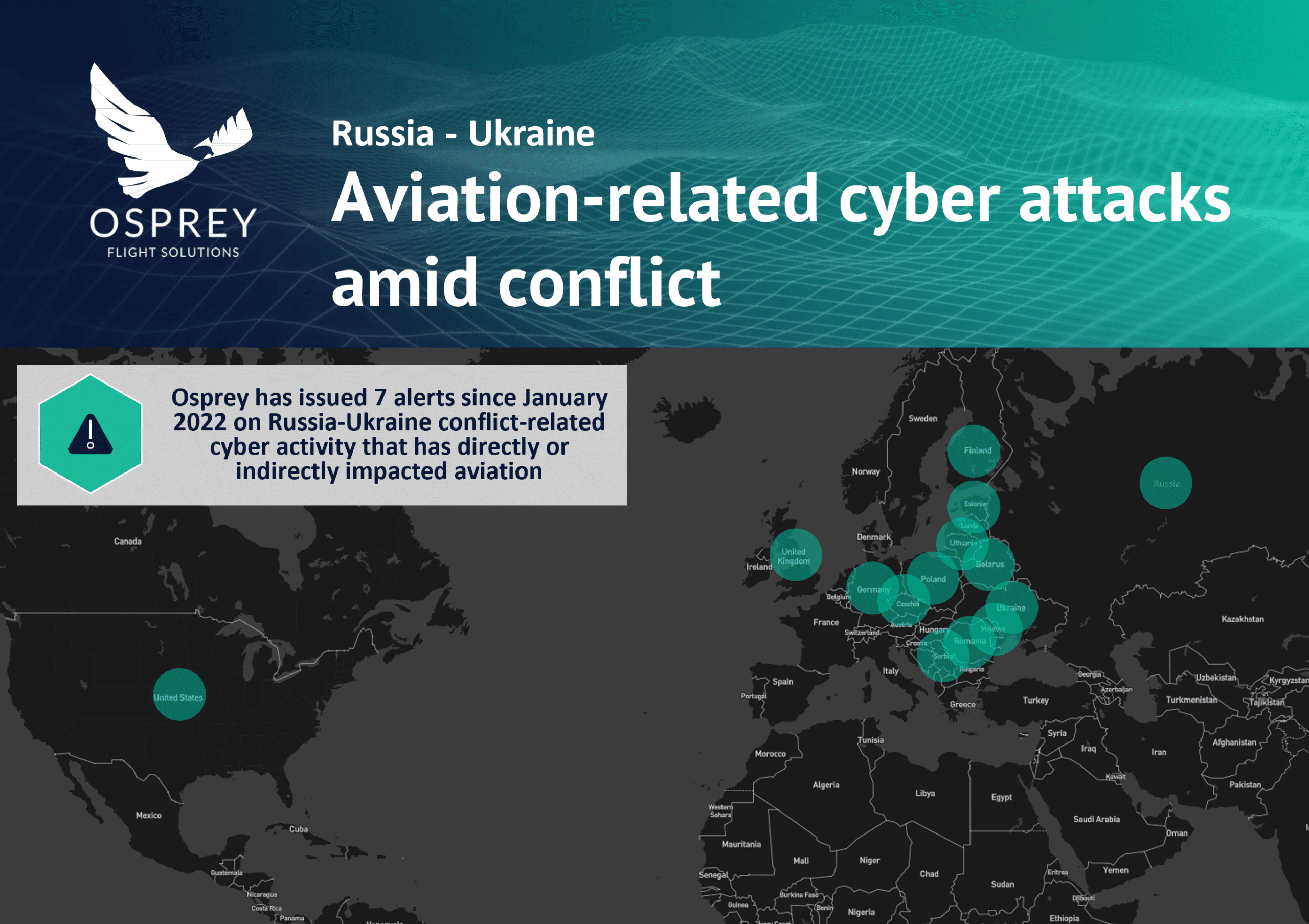
In the period leading up to and following Russia’s invasion of Ukraine, which began on 24 February, cyber attacks targeting public and private entities in countries both directly and indirectly involved in the conflict have been reported frequently. Such attacks, which have been attributed to both state and non-state actors, have included phishing and malware campaigns as well as distributed denial-of-service (DDoS) attacks. Russia has been accused of conducting a “hybrid war” against Ukraine through the use of cyber attacks alongside conventional military activity. The aviation sector has not been untouched by the cyber activity that has surrounded the conflict; Osprey Flight Solutions has been tracking and alerting on cyber threats that directly and indirectly impact aviation-related entities. In particular, Osprey has alerted its clients to the ongoing activities of a Russian hacker group, known as ‘Killnet‘, which has conducted DDoS attacks targeting airport websites, among other targets, in several countries that have expressed support for Ukraine.
According to the US-based web performance and security company Cloudflare, a DDoS attack is “a malicious attempt to disrupt the normal traffic of a targeted server, service or network by overwhelming the target or its surrounding infrastructure with a flood of Internet traffic”.
Who is ‘Killnet’?
Killnet is a Russian hacker group and self-proclaimed “hacktivists” – those with a political or social motivation for hacking. Killnet uses a Telegram channel to make announcements regarding its activities; its first post was on 23 January. Since then, the group has claimed DDoS attacks targeting the websites of various public and private agencies, including government ministries, in a number of countries. In attributing a series of DDoS attacks targeting the websites of Moldovan public authorities on 1 May to Killnet, Moldova’s Security and Intelligence Service (SIS) claimed that Killnet “specialises in carrying out DDoS attacks on countries considered by them to be supporters of Ukraine”. Exemplifying this, in recent weeks, Killnet has claimed targeting government ministries in Germany, which Killnet stated was in response to Germany supplying Ukraine with weapons; Lithuania, which is reported to have supplied Ukraine with man-portable air-defence systems (MANPADS); and Poland, which has provided notable humanitarian and defence weaponry support to Ukraine.
In the past two months, Killnet has claimed attacks targeting the websites of more than 30 European airports in Germany, the UK, Poland, the Czech Republic, Estonia, Romania and Latvia, as well as a US airport. In these instances, Killnet has either claimed conducting the attack itself or has attributed it to one of its affiliate groups. The first airport attack claimed by Killnet was on Connecticut’s Bradley International Airport (KBDL/BDL), in the US, in late March. Killnet has not stated why it has chosen to target airport websites; however, a number of the airports targeted (although not all) are state-owned and, as such, targeting them reflects the group’s apparent aim to retaliate against government support to Ukraine. Also of note, Killnet has called for supporters to join its cyber activities; recently, on 7 May, Killnet announced that US-based supporters had conducted an attack targeting the US-based aerospace company Boeing.
The potential impacts of a DDoS attack are dependent on the target of the attack. In the examples outlined above, there has been no reported impact on the operational status of the entities targeted, except for disruption to their websites. Killnet has previously stated that its attacks have shown how “easy” it is to cause inconvenience. However, depending on the function of the server targeted, a DDoS attack could have a significant impact on an entity’s operations. Moreover, there is the potential for DDoS attacks to be used to obfuscate more nefarious cyber activity. Notably, on 23 February, the day prior to Russia’s invasion, several Ukrainian state and banking websites were subject to DDoS attacks, which were thought to have been conducted by threat actors linked to Russia. Later that day, it was detected that after the attacks, a type of wiper malware – a destructive malware that erases the content of an infected device’s hard drive – had been installed on a number of Ukrainian devices. However, at this stage, there has been no indication of this occurring in an attack targeting an aviation entity.
Cyber attacks on both sides of the conflict
Cyber attacks targeting entities on the opposite side of the conflict – including Russia and its allies – have also been reported in recent months. For example, in early March, it was reported that the websites of Sochi (URSS/AER), Krasnodar (URKK/KRR) and Anapa (URKA/AAQ) airports in Russia had been subject to DDoS attacks; however, there has been no reported claim of responsibility for the attacks. More recently, on 13 May, the websites of a number of Russian airports – some reports indicate as many as 30 – as well as several Russian airlines, including Rossiya Airlines, Smartavia, Yakutia Airlines, ALROSA, Yamal Airlines, Izhavia and Aurora, were subject to DDoS attacks. The attacks targeting the airlines were allegedly in response to Moscow’s decision to keep foreign leased aircraft in Russia.
Russian entities have also been subject to cyber attacks that have been claimed by ‘Anonymous’, a hacker collective that previously declared “cyber war” on the Russian government following the invasion of Ukraine. Anonymous claimed to be responsible for a cyber attack that targeted Russia’s Federal Agency for Air Transport (FAVT, known as Rosaviatsiya) in late March that resulted in the erasure of FAVT data and disruption to the agency’s operations. Cyber attacks targeting Russia and Ukraine, as well as their allies, highlight that threat actors are seemingly conducting attacks based on rival pro-Russia versus pro-Ukraine agendas, and aviation entities – including airports, airlines and civil aviation bodies – have been identified as valid targets. A similar trend has also been noted – and reported on by Osprey – in instances of bomb threats targeting airlines and airports amid the Russia-Ukraine conflict.
Cyber Advisories
Amid heightened tensions between Ukraine and Russia – including prior to and during Russia’s invasion of Ukraine – several national cybersecurity agencies have issued advisories for malicious cyber incidents, including warning of potential Russian state-sponsored cyber threats.
On 20 April, a joint cybersecurity advisory (CSA) was issued by the cybersecurity authorities of Australia, Canada, New Zealand, the UK and the US regarding Russian state-sponsored and criminal cyber threats to critical infrastructure. The CSA noted that “Russia’s invasion of Ukraine could expose organizations both within and beyond the region to increased malicious cyber activity”. The advisory states that such cyber activity may be conducted in response to economic sanctions imposed on Russia in response to its invasion of Ukraine, as well as “materiel support” (military materials/equipment) provided by the US and US allies and partners. Through their ‘Shields Up‘ initiative the US Cybersecurity and Infrastructure Security Agency (CISA) has also collated its updates and guidance for organisations with regard to current cyber threats resulting from the Russia-Ukraine conflict.
Separately, on 5 May, the European Union Aviation Safety Agency (EASA) published a “Review of Aviation Safety Issues Arising from the war in Ukraine” that outlined 20 issues that have been identified in seven areas:
- Security
- Infrastructure and Equipment
- Air traffic management and navigation service provision
- Human performance
- Management systems
- Energy crisis impact
- Health and Environment
Under ‘Security’, EASA identifies “an increase in cyber-attacks associated with the conflict” as a safety issue; however, it was not specified how such cyber attacks pose a safety issue to aviation.
A persistent threat
As the Russia-Ukraine conflict persists, cyber attacks related to the conflict are expected to continue; Killnet recently announced that it plans to launch further attacks targeting the US, the UK, Germany, Italy, Latvia, Romania, Lithuania, Estonia, Poland and Ukraine. While the effects of the DDoS attacks against aviation-related targets to date have been limited, a cyber attack – including a DDoS attack – has the potential to have a significant impact on an entity’s operations. Also, as part of critical national infrastructure, disruption to aviation operations via a cyber attack could have a much wider impact beyond the aviation environment. As a result, aviation entities are also likely to continue to be among the victims of attacks, particularly those in countries that have expressed support to Ukraine. While attacks have largely been directed at airport websites, airlines – particularly those that have been involved in delivering humanitarian and defence supplies to Ukraine – and civil aviation authorities may also be targeted. Aviation entities should undertake a continuous review of cyber threats to their operations and ensure that measures are in place to mitigate the impacts of a potential attack.