The problem
While risk analysis is a significant aspect of the aviation security industry, it still relies to a great extent on a human-based process. The fundamental flaw with this approach is humans are inherently subjective in their understanding of a situation. This undermines the accuracy of the three most important pieces of the risk analysis puzzle: threat identification as well as likelihood and impact quantification. The problem is that if you put two independent people in exactly the same situation, they will each have a different perspective. So, how can we expect our analysis to be consistent, objective or accurate when it depends completely on who is conducting it?
Time constraints, bias and the focus on current intelligence production all play a major factor in the current analytical culture within the aviation security industry. Time constraints on intelligence reporting can lead to a lack of necessary data required for complete threat identification and security risk analysis. The lack of data leads to assumptions that are skewed by the bias of the individual analyst. Also, there is a trend within the industry to focus on current intelligence reporting – writing reports and producing PowerPoint slides – rather than multi-source threat identification and security risk analysis. In short, the industry focuses its time and efforts on a ‘whack-a-mole’ posture of securing day-to-day operations rather than developing systems that can continuously improve over time.

Developing a comprehensive and objective understanding of an environment, particularly in an increasingly complex world, is hard. In fact, it is more than hard. It is impossible for a human, with all the bias and subjectivity inherent in each unique combination of education, culture and experience, to make that objective, consistent analysis. Within the aviation security industry, this is compounded by the sheer operational tempo – when you cannot conduct an objective analysis of the risks for one flight, what do you do when faced with thousands a day? The answer is that many organisations do not even try, and those that do consistently struggle to implement a process that adds real value to their operation.
There is a solution. Osprey Flight Solutions’ experience shows that embracing artificial intelligence (AI) and combining it with human expertise is the only way to overcome the above challenges. These capabilities offer huge opportunities to the aviation security industry.
The solution
The use of AI techniques has allowed the Osprey analysis team to create a more resilient, objective, consistent, dynamic and comprehensive picture of the global aviation operating environment. AI enables Osprey to produce faster, more accurate analysis, resulting in improved decision making by our clients to mitigate a broad spectrum of risks in a timely and scalable fashion. Proper and effective risk analysis should and does add huge value. It is an essential component of operational and, in fact, commercial success.
Osprey is changing the analytical culture within the aviation security industry from an individualistic and purely human-based approach to a more streamlined, data-led analytical methodology for threat identification and security risk analysis. It is only through the use of AI-enabled data collection and analysis coupled with highly skilled human analysts that we have achieved this. These capabilities offer huge opportunities, and we are dedicated to continuously improving the ways in which we support the aviation security industry.
Automated categorisation, multi-source corroboration, geolocation and date/time stamping are the fundamental components of the data-led risk analysis system developed by Osprey. These all require AI capabilities to be effective and accurate. The continuous and automated improvement that machine learning enables ensures that our systems, analysis processes and analytical methodologies can, extremely quickly, become significantly more capable and more accurate, with little or no drain on resources.

Osprey’s AI-enabled information collection tools gather data from a very broad spectrum of sources. Such sources include social media platforms, major international media outlets, local news publications, national-level authorities, law enforcement, government departments, industry organisations, special interest groups with a focus on aviation, think tanks and third-party intelligence providers. Using advanced computing techniques, our tools gather data every few minutes from hundreds of thousands of open sources in dozens of different languages. When combined with Osprey’s specialist team of analysts, we ensure that at any one time there is an objective and consistent picture of the global aviation operating environment.
How Osprey does it
The AI techniques implemented by Osprey within our system significantly enhances capacity within the following three key areas:
- Analytical methodology automation
- Incident database development
- Collection management
All three areas are crucial to the future of aviation security and risk analysis. We focus our AI techniques on timely and accurate qualitative reporting of aviation security incidents supplemented by robust analyst-driven risk assessments, long-term trend analysis and tailored data-collection models. Below are several key outputs of the integration of AI and machine-learning techniques within the Osprey system.
Analytical methodology automation
- Cutting-edge, instantaneous operational aviation security risk assessment methodology
- Near real-time risk scoring updates via automated criteria benchmarking and machine learning
- Direct, instantaneous access to operational aviation security risk assessments and data analytics
Incident database development
- Reporting combines human expertise supplemented by machine learning analytical techniques
- Geospatial and quantitative aviation security incident structuring to facilitate predictive analysis
- Automated web scraping of multi-source verified and coded aviation security incident data
Collection management
- Exploitation of aviation security keyword trends on social media and internet search platforms
- Geospatial mapping and modelling of incident data intensity levels for historical trend analysis
- Analytics and mapping of aviation security keywords in traditional media via big data querying
The example
The Osprey Flight Solutions team continues to closely monitor the Russia-Ukraine situation. In the spirit of information sharing, we produced a publicly accessible Google Map compiled by our analysis team and the AI-powered Osprey system, which provides a notional overview of Russian and Ukrainian air-defence deployments, shown below:
Map displaying an estimated overview of Russian & Ukrainian SAM system deployments
How did Osprey do it? We leveraged our system with the technology described above, employed AI techniques and tasked our analysts with building a solution. The Russian and Belarusian surface-to-air missile (SAM) site locations were based initially on two sources. The Osprey system exploited social media, Russian military reports and commercial satellite imagery data to project the rest of the Russian and Belarusian deployments.
Osprey also used the Stockholm International Peace Research Institute (SIPRI) arms transfer database and found that Ukraine had 15 battalions of S-300 air-defences and eight battalions of S-125V systems. Two S-300 battalions were lost to Russia in Crimea in 2014, leaving Ukraine with 13, of which 11 are serviceable and deployed, according to Ukrainian military data.
Looking at where Ukrainian military bases and critical infrastructure are located, the Osprey system used AI techniques to identify notional deployment sites in Ukraine for S-125V systems. An intelligence report by Estonia (a NATO member) aided this process.
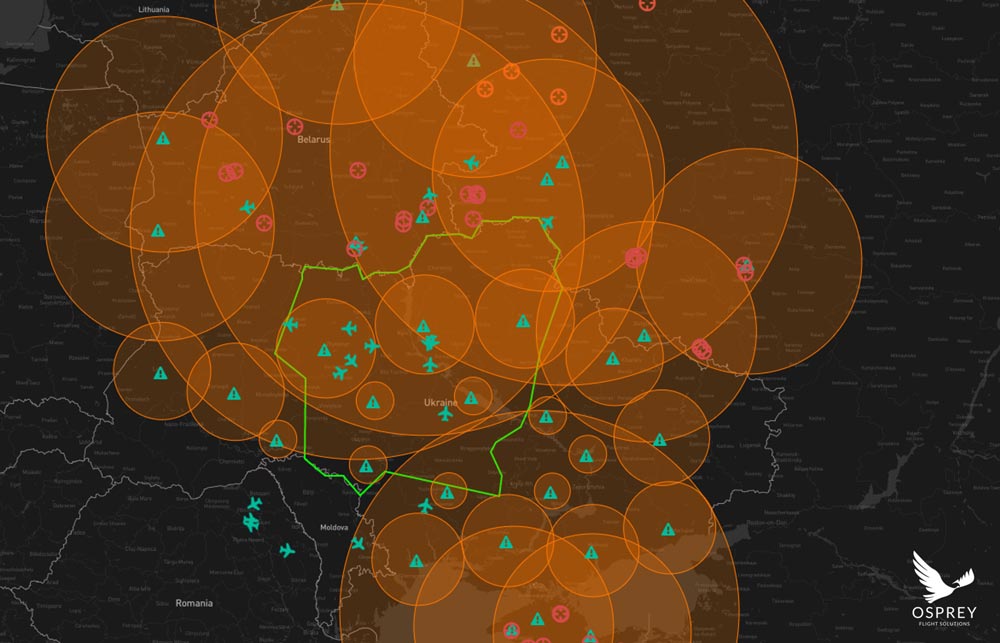
Caveats of the maps:
- Tactical air defences, of which both Ukraine and Russia possess a variety, are not included. For example, KUB, Osa, BUK (all variants), Tor, and Pantsir air defences are not depicted as they are all highly mobile. Additionally, MANPADS, of which Russian and Ukrainian forces have a plethora, are not depicted.
- Ship-borne air defences in the Black Sea, which both Russia and Ukraine possess, are also not included.
The above is aviation security-centric open-source intelligence powered by AI and curated by specialist human analysts. It is what the Osprey Flight Solutions analysis team does each and every day.
Why it matters
There is always a crisis. The threat actors are continually evolving. The environment changes. Trends shift. Patterns emerge. But a solution exists. Osprey is looking to the future with wide eyes and embracing the use of AI techniques to better understand — and continuously improve that understanding — of the global aviation operating environment, the risks present and the measures that need to be taken to ensure that everyone is as safe and secure as possible when travelling by air.